Vulnerability Management Using Threat Models And Attack Graphs

Vulnerability Management Using Threat Models And Attack Graphs
Vulnerability Management Using Threat Models And Attack Graphs
Introduction to Attack Graphs
When the goal of hardening network security meets the reality of budget constraints, security architects need to apply resources strategically. Risk management calculation involves merging threat level and Probability of incident occurrence. In defending a network against a cyber-attack, determine what risks may be acceptable in the wake of substantial mitigation. However, Probabilistic Threat Modelling with Attack Graphs can support making value-based decisions on how much protection and where to apply it.
Compromising a network and exfiltrating data or disrupting data integrity is not a one-step process. Combination Attacks involve exploiting multiple vulnerabilities together, and Vulnerability Chaining is required for deep network penetration [1]. Attack Graphs model how an attacker could conduct a chained attack sequence to compromise a high-value target. Mapping Exploit Dependency helps highlight the attack sequences that are most likely based on the nature of vulnerabilities in the network.
Attack Graphs reveal attack sequences by enumerating potential attack vectors and inter-connecting attack surfaces between endpoints. Probability Modelling can further insight into managing risk strategically by modeling attack flows determining the possible pathways. Decisions to allocate resources, remediate vulnerabilities, and plan for incident response can be enhanced by considering the results of Attack Graphs and Probability Modelling. In addition, novel modeling techniques incorporating newly available information and metrics can improve existing models and provide deeper insights.
Building An Attack Graph
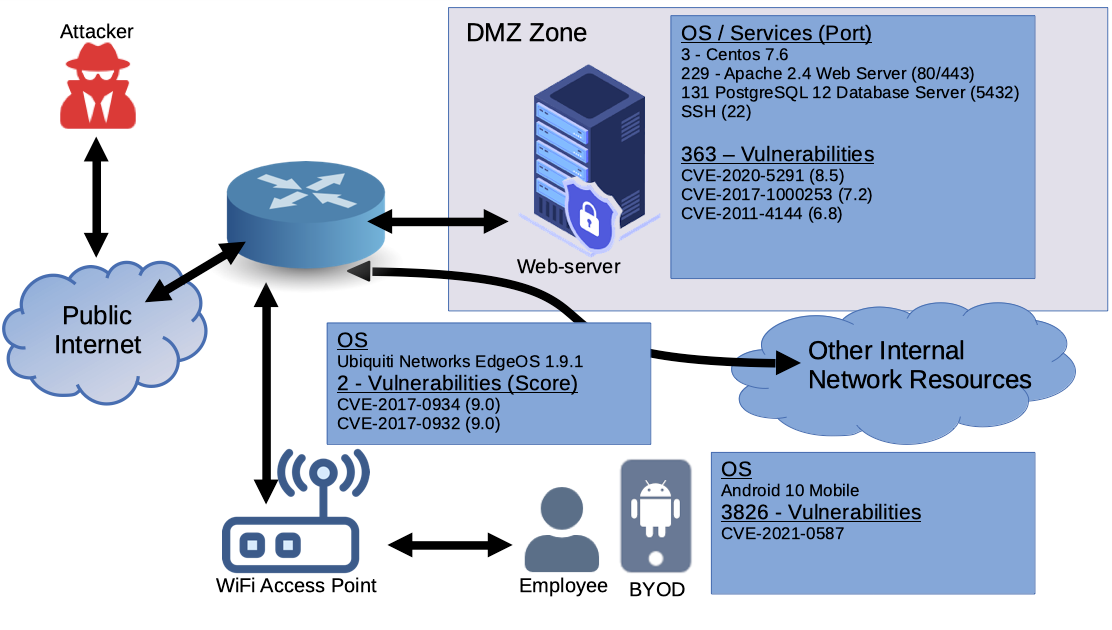
An initial condition for building an Attack Graph is documenting a comprehensive network diagram including all endpoints and hosts as nodes and their inter-connectivity as the vertex. In the second stage, all OSI Network Layers Model layers should be consulted when building a thorough threat profile for each host. For example, in Layer 1, the Physical Layer would include all physical access to critical appliances and consider whether unused Ethernet jacks can receive an IP address on the network. Layer 2, the Data Link Layer, would consider VLAN hopping, ARP, and MAC spoofing, as well as other reconnaissance techniques that utilize discovery protocols. Finally, layer 3, the Network Layer, includes vulnerabilities including DNS spoofing, IP spoofing, malformed packets.
To achieve a quantitative threat profile, existing Attack Graph and Probability Modelling research have applied Common Vulnerability Scoring System (CVSS) to assess the severity of identified vulnerabilities. Common Vulnerability Exposure (CVE) can be mapped to endpoint nodes using the Common Platform Enumeration (CPE) to match CVEs with OS, port-based services, and software applications installed on each system. The Common Vulnerability Scoring System (CVSS) enables risk quantification using a set of Base, Temporal, and Environmental Metrics.
Base metrics include Attack Vector requirements (network, adjacent network, local, physical), Attack Complexity requirements (low, high), Privileges requirements (none, low, high), User Interaction requirements (Boolean), and potential impact on a host’s Confidentiality, Integrity, and Availability.
Temporal Metrics can contribute to identifying the Probability that an attack will happen against a given vulnerability and strategic decision making. For example, exploit Code Maturity Metric (existence unknown, proof-of-concept code, functional exploit, advanced functional code) makes it possible to quantify how readily available exploit code can be found by an attacker. In addition, the remediation Availability Level Metric (official fix available, temporary fix, workaround, and unavailable) helps identify whether the vulnerability is patchable against exploitability. This contributes to determining the remediation cost and helps support strategic decisions on allocating resources.
CVSS v3 includes Environmental Score Metrics that can contribute to determining the possibility and Probability for exploit chaining. In addition, impact Score Modifiers (Confidentiality / Integrity / Availability requirements) define pre-conditions that must be met to exploit the CVE. CVSS metrics are compiled into a score between 0 and 10 representing risk severity, which is assigned to each CVE but can also be input into a simulation model individually as variables.
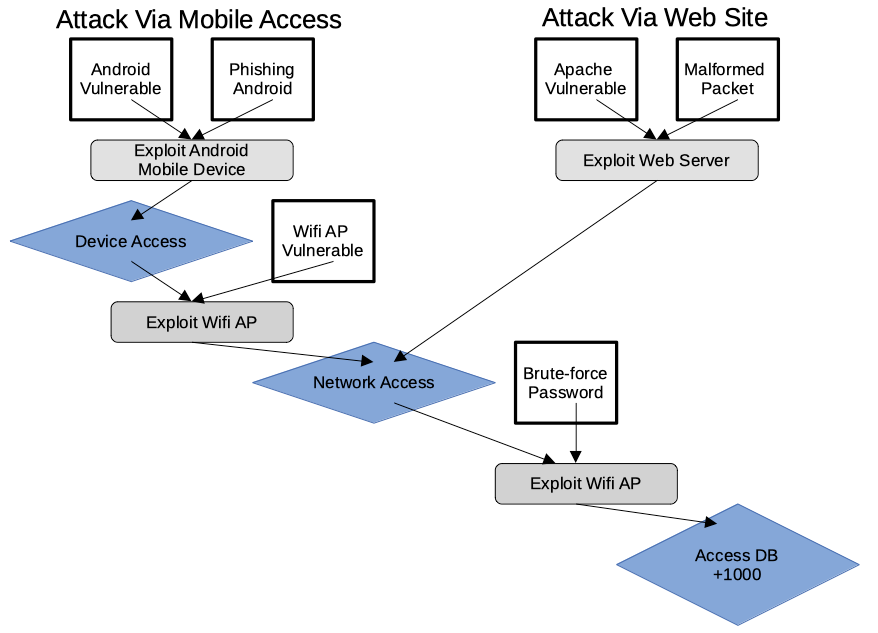
Below is a basic network scenario used to build a simple Attack Graph. In the design, a router gives mobile devices access to the internet network and allows public access to the webserver. Also, an employee is shown accessing the network via a mobile device running Android. OS and services are listed along with the associated cumulative number of CVE vulnerabilities and their ID numbers and scores. In Diagram 2, a basic Attack Graph shows two of the numerous possible exploit chain sequences that an attacker could take to access the data stored on the webserver. Although it is plausible that other high-value targets would be available on a corporate network, this simplification serves to exemplify an Attack Graph.
Probabilistic Modelling
Probabilistic Modelling generates threat intelligence by simulating attack sequences and their impact at subsequent stages in an offensive campaign. Statistical methods combine CVSS metrics and apply randomization to produce statistically likely attack vectors and series of events. As a basic example, CVSS Temporal Metrics Exploit Code Maturity and Remediation Availability imply a combination of how difficult a CVE would be for an attacker to compromise and how easily the vulnerability can be patched.
The most common models used are Stochastic Markov Modelling which simulates sequential states within the mapped network system and how an attacker’s behavior will change as each successful compromise changes vulnerability state conditions. Bayesian Networks have also been used to model conditional dependence to determine the most likely exploit paths in a network. Conditional dependence is helpful to simulate the real-life circumstances of exploit chaining; that exploits may depend on conditions that another exploit can create. For example, a remote code execution vulnerability may depend on high-level privileges, which can be gained by exploiting another vulnerability that allows partial integrity impact. Bayesian Modelling allows for these dependant circumstances.
Quantification of network security risks allows strategic decision-making for vulnerability management. Allocating time and resources wisely increases the value of implemented security measures. Attack Graphs provide risk-based insight into potential pathways an attacker could take towards identified high-value goals, and when combined with Probability Modelling, the most threatening paths become quantitatively obvious and can be hardened and monitored closely.