Security Solutions
Cybersecurity for NexGen Business Enterprises - A Titanium Backbone for Every Organization
Security Solutions for Unique Challenges
The dawn of the digital era brought forth a transformation unlike any other. As industries, businesses, and individuals became more interconnected, an intricate tapestry of networks, systems, and digital platforms emerged. With this shift, the world witnessed the rise of unprecedented opportunities and the advent of complex digital vulnerabilities.
Cyberattacks, once a matter of isolated incidents, have now transformed into pervasive threats, casting shadows over every aspect of the digital domain. From financial sectors facing sophisticated heists to healthcare organizations grappling with data breaches, no sector remains untouched. The cyber threat landscape, characterized by its ever-evolving nature, exhibits a diverse array of attack vectors, including Advanced Persistent Threats (APTs), Distributed Denial of Service (DDoS) onslaughts, and zero-day exploits, to name a few.
fnCyber learns by mapping Business Goals and Objectives to its IT Systems Security Risk, Policy, and Governance Landscape, deriving a Baseline along with existing controls and, after that, improvising the existing internal IT security controls without altering the eco-system to maximize the ROI of the current infrastructure.
With these enterprise dynamics increasing the stakes, fnCyber emerges with robust and comprehensive cyber security solutions with Integrated IT Security Risk Management. The aim is to capitalize on the IT Systems Security Risk Management strength and outline how Enterprise IT Systems Security Risk is distributed across the Organization's Operational and Compliance elements, thereby drawing Benefits, Value, and ROI. fnCyber Security Solutions also drives a Security Risk-Aware Culture to ensure risk is addressed till the last mile.
The Service Approach
The cybersecurity terrain is ever-evolving, necessitating robust solutions to tackle emerging threats. Recognizing the intricate web of technology and operations within organizations, fnCyber's Security Solutions Service takes up a thorough discovery and design phase. This stage demands a comprehensive understanding of the organization's technology landscape, data flow patterns, and the operational nuances that define the business. Such in-depth analysis provides a clear vantage point to identify vulnerabilities, not just in traditional IT infrastructure but extending to cloud platforms, endpoints, web applications, and beyond. As unique as the organizations, these solutions absorb the specific challenges of different domains. Whether it's strengthening remote access protocols, enhancing container security, or designing formidable perimeter defenses, each solution bears the stamp of customizability.
These Security Solutions Services aim to safeguard digital assets, necessitating a proactive, multi-faceted strategy. Initiating with Insider Risk Management, the process delves into User and Entity Behavior Analytics (UEBA), flagging anomalies in user actions. With a surge in remote work, Remote Security Management becomes paramount, incorporating Virtual Private Networks (VPNs) and Multi-Factor Authentication (MFA) to ensure secure and authenticated access. On-premise infrastructure Vulnerability Management then identifies potential weak links in local networks and systems, integrating tools like IDS and IPS to counteract breaches preemptively.
In any organization, decisions are made in a layer and executed at a different layer; hence, the most critical aspect of Integrated Security Solutions Services is to explore various security strategies with all their advantages and disadvantages, deploy optimum controls in line with the Business Owners Risk Perception and agreement with other stakeholders. Critical Success Factors would include benefits measurements against goals such as business to explore a range of opportunities, Manage Entity-Wise Systems Risk, IT Support, and Performance. The Integrated IT Security Solutions includes extensive facilitation and brainstorming sessions, constantly engaging all the stakeholders in every phase to establish one risk view across the organization.
The Phases
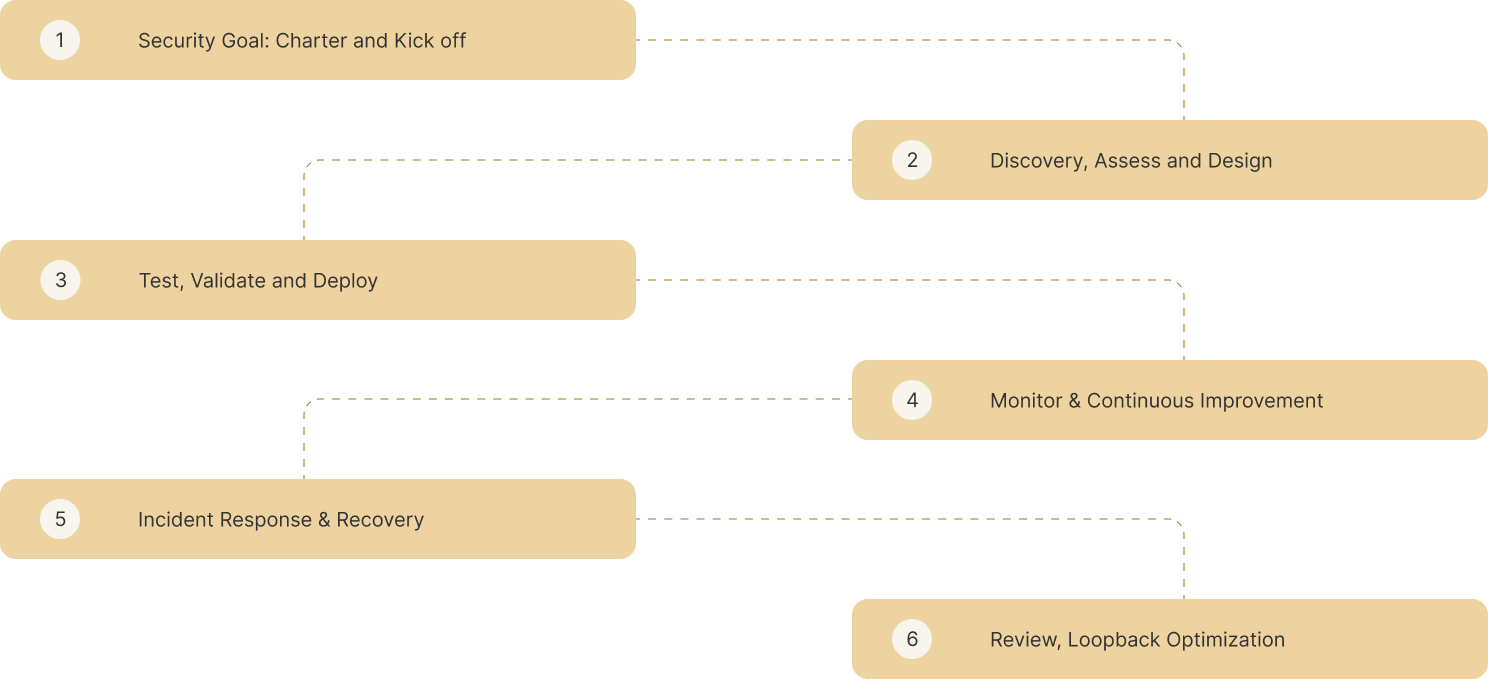

Transitioning to the cloud, fnCyber Security Solutions Services brings a discreet set of expertise in the domains of Cloud Security Posture and Vulnerability Management and employs Cloud Access Security Brokers (CASBs) and Cloud Workload Protection Platforms (CWPPs) to provide visibility and control over data. Endpoint Security & Vulnerability Management integrates EDR solutions, ensuring devices connecting to the network remain uncompromised. Given the pervasive nature of web transactions, Security Solutions Services for Web-App / Website Security Management emphasizes Web Application Firewalls (WAFs) and Regular Application Security Testing (AST), which provide robust defense mechanisms.
Select & Explore the Security Solutions
"Envision Multi-Dimensional Growth With Integrated Security Solutions"
Resources

Articles
Security Strategy Intelligence - Practices and more


Case Studies
Realworld Business Challenges - Keep it Targeted and Simple


Archives
Infrastructure Security - What makes it so critical


Contact Us

fnCyber Security Consulting Services Pvt. Ltd., Level 1, Salarpuria Knowledge City, InOrbit Mall Road, HITEC City, Hyderabad, Telangana 500081 India

fnCyber Security Consulting Services B.V., 6th Floor, HSD Campus Wilhelmina van Pruisenweg 104 2595 AN Den Haag
+31(0)70 2045180

