Security Assessments
Self-Aware Preparedness is the Best Defence Against any Threat
Security Assessment is Foundational
Many governments, banks, tech giants, and research labs have launched various campaigns addressing the importance of cybersecurity because the net has already sprung, and once programmed attacks are automated with bots and scripts without human intervention. In today's world, cyber threats are not just probable but inevitable. Cyber Assessments serve as the bulwark, ensuring that digital sanctums remain uncompromised.
fnCyber designed a security-centric Cyber Assessment as a Service Strategy to be adopted proactively rather than enforced, driving the goal of creating Self-Aware Organizations to prevail in the long run. Security Assessments stem from the growing realization of the intricate vulnerabilities within the digital realms of organizations. As technology integrates deeper into operational frameworks, the potential points of exploitation multiply. These assessments have become a cornerstone in understanding and mapping the digital vulnerabilities of an entity. Only then any Security Assessment Program will bring meaning to its purpose, which is the core philosophy of fnCyber.

The Service Approach
Our practice takes the form of a service that originates from a blend of digital forensics, cybersecurity protocols, and the continual race against hackers seeking system weak points. The security risk assessments shed light on the most susceptible aspects of an organization's cyber infrastructure by systematically evaluating networks, systems, and applications. Over time, the methodology has been refined to incorporate advanced tools and techniques, shaping it into a service that responds to the ever-evolving threat landscape. The essence of these assessments lies in detecting and anticipating potential threats, ensuring that organizations remain several steps ahead in cybersecurity. Finally, align all aspects of the assessment with the corporate vision and strategy to design and implement the improvement plan.
fnCyber Security Assessments delve into the intricacies of an organization's digital framework, spotlighting vulnerabilities and emerging threats. This rigorous examination evaluates the robustness of networks, systems, and applications in withstanding cyber-attacks. Essential techniques, such as attack surface mapping and deep vulnerability scanning, form the core of these assessments. Highlighting system weak points, the assessments enable prioritization of critical areas, facilitating the design of effective remediation strategies. As the digital landscape witnesses increasingly complex threats, these assessments emerge as pivotal in ensuring persistent adaptation and safeguarding of digital assets. Beyond mere technicalities, the process also encompasses evaluating policies and procedures to ensure alignment with the best industry standards—the ultimate goal: a fortified, vigilant digital environment resilient against evolving cyber challenges.

The Phases
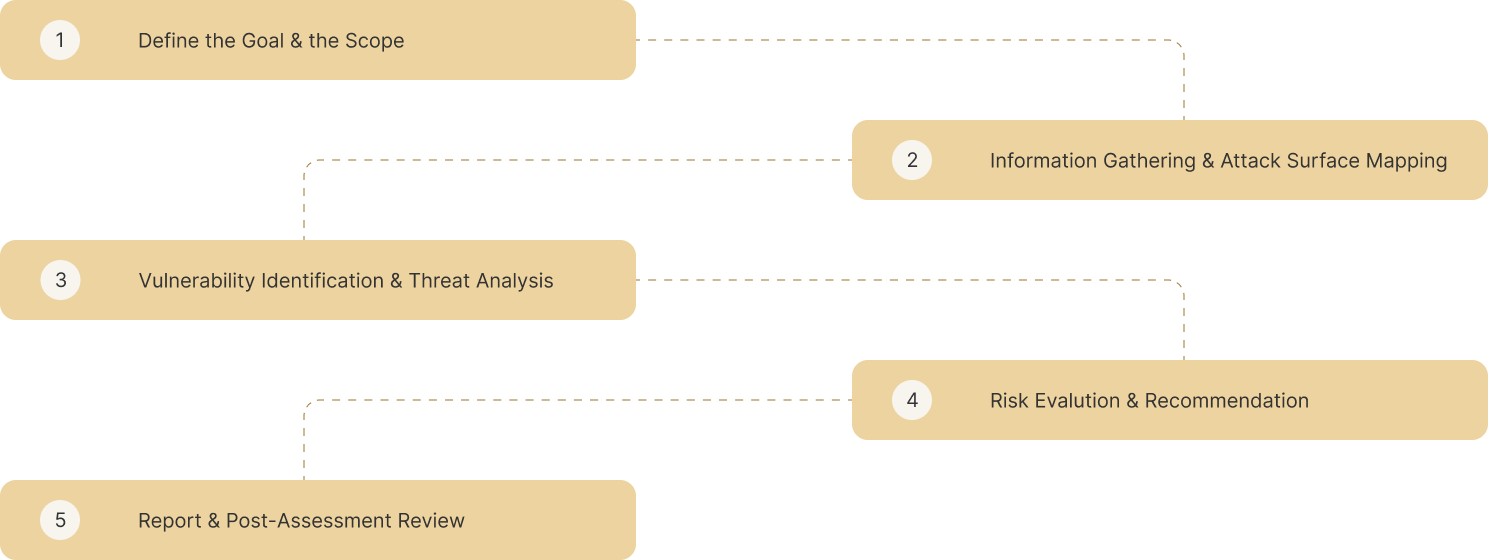

With a long-term commitment, fnCyber has all the tools for the trade to conduct attack simulations and effectively carry out campaigns to Improve Organizational Resilience via Cyber Security Assessments.
Select & Explore the Security Assessments
"Security is as Strong as the Weakest link in the Chain. Cyber Assessments can Address 57% of Total Breaches."
Resources

Articles
Security Strategy Intelligence - Practices and more


Case Studies
Realworld Business Challenges - Keep it Targeted and Simple


Archives
Infrastructure Security - What makes it so critical


Contact Us

fnCyber Security Consulting Services Pvt. Ltd., Level 1, Salarpuria Knowledge City, InOrbit Mall Road, HITEC City, Hyderabad, Telangana 500081 India

fnCyber Security Consulting Services B.V., 6th Floor, HSD Campus Wilhelmina van Pruisenweg 104 2595 AN Den Haag
+31(0)70 2045180

