The 3 must have Cybersecurity Roles In your Organization

The 3 must have Cybersecurity Roles In your Organization

Tag a Name - Who Owns Information Security in your Organization?
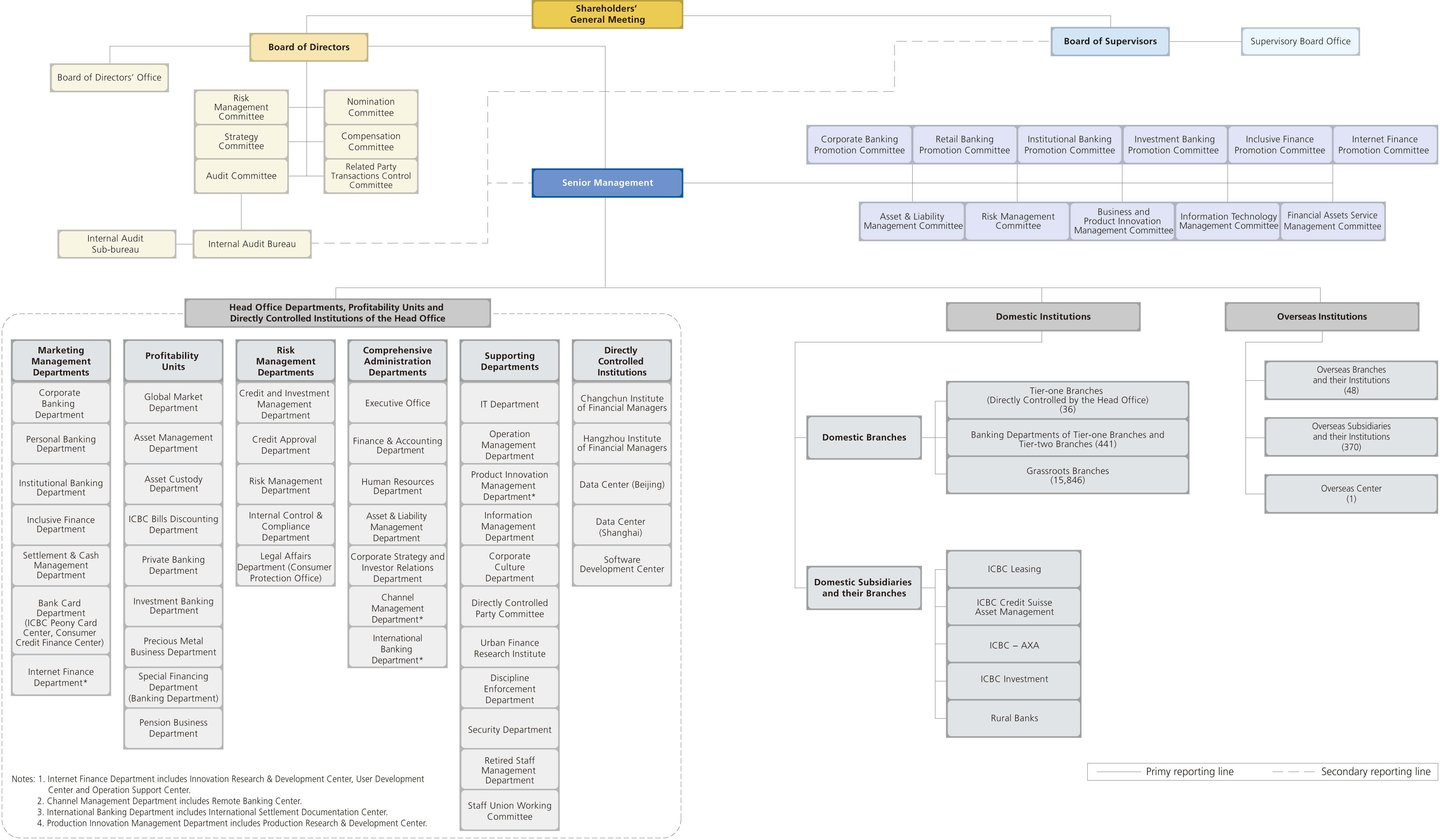
A random search on some top insurance companies gave a good insight into their Organization Structure; One Company has a Chief Information Officer and another a Chief Risk and Investment Officer who went onto become a Chief Financial Officer with M & A background and of course hardcore experience of their respective domain but not Information Security or more so Cybersecurity - and they are one of the top insurance agencies in the world. Can you locate the CISO or perhaps a CIO in the picture below. All I could pin point are: 1) Risk Management Departments - Credit and Financial Risk; 2) IT Department and Information Management Department as some of the Supporting Departments and 3) Information Technology Management Committee as a part of the senior management. The like offices of CIO or CISO are not to be seen and this Org Structure which belongs to a $ 4 Trillion Bank.
One of the worlds richest and most admired computing device manufacturer has no mention of such a role in the Executive Body; company has a CEO, COO, CFO and a General Counsel along with others and that's it. Don't Worry, CIO / CISO - Not Important or not needed at the C-Suite level. If this is the nature of the highly regarded institutions what could be the fate of others; Not sure what happened when these were reported: Incident of the Week or may be Spying Incidents. Do we still say these roles are NOT IMPORTANT in the Digital Age. As per George Washington University Study: Those in need of Cyber Task Force are Technology and Internet companies, Security software companies, Government departments and Defence/Intelligence agencies, IT companies, Industrial sectors, The E-Commerce sector, BFSI etc but we have seen some random set of such companies in the examples above.
While there were about 42000 incidents reported in the Verizon DBIR with an average cost of a breach is about $ 3.92 Million then the over all costs of 42000 incidents adds up to.... No point trying simple math here.
Now with the above situation in 2019; it may not appear to be a good investment or at least not justified enough to have a InfoSec or Cybersecurity Department in any organization. Regardless, has there ever been a thought given at the board or Governance level if not please do spare some more time to read through. Whether or not the Enterprise is new to Cybersecurity: There must be an accountable individual who would hold the overall responsibility of Security Governance. That would be the First-Must Cybersecurity Role at the Strategic level:
Chief Information (Security) Officer:
Did we say Dedicated CISO? This is where the ball gets dropped; the organization may not see a need for a dedicated CISO and would not even want to consider the option in the first place and drop the Cybersecurity Philosophy as a whole. And the Alternative is vCISO; yes a CISO on a contract; for a fact that CISOs are Virtual Professionals who do not need to visit the premises unless otherwise needed. As with any contract; most of the contractual resources have to justify their expertise and the same applies here; meaning the CISO would be an accredited one who can help the organization in establishing a Security Program and help assign a sound Cost Benefit Analysis to allocate desired budgets. There are many organizations offering vCISO services who can help establish a framework - The Skeleton on which Security of the organization would rely on.
Information (Security) Architect:
The Second-Must role required for any Organization. As such the job of an Architect is to Create a Model/Design/Structure as per the requirements - so a One Time Job to begin with unless the model/design is subjected to a constant change which is again unlikely. Assuming there is a CBA justifying the Security Investment along with a ROSI Plan; requirements should have been clear by this stage. Here is where to leverage the Industry Expertise of Technology and plethora of Security Applications and Services. It would be the best approach to contract this specialist job to a specialist itself. Also when you contract a company you are actually engaging an Organization to deliver for your needs. Here is a list of 500 to begin with and fall back to rely on your sound financial decisions and legally binding contracts.
Cybersecurity Specialists: Engineer/Analyst/Responder:
Third-Must role required is the specialist category operational staff. Before that; we are in the Digital Age and without a doubt technology has advanced leaps and bounds. Consider the Intelligent deployment of technology resources; explore monitoring solutions a combination of controls as such. If the Architect has such a model in place engaging technology with an integrated approach to address monitoring needs; most of which is pretty much automated. Its unlikely that any organization will witness threats or incidents on a daily basis; but definitely requires constant monitoring which is best left to automation.
It can be a daunting task to manage the security of the organization as an additional responsibility of the other C-Suite officer; but oversight of one of the executive is a must. The tiered support Cybersecurity structure can definitely help the organization achieve its objectives in the long run. A good add on would be the timely implementation of Awareness campaigns, review and reinforce them from time to time.
At the end, if Cybersecurity and everything else around it seems like a nightmare, no one is to be blamed for the state of affairs. The Last in the list to explore is Cyber-Insurance or otherwise called as Cyber Liability Insurance Coverage is your organizations Bail Out option. The Security Posture is much better off at the end if not at the beginning of this Article.